Boletín Semanal
08 de junio de 2024 a 14 de junio de 2024
7
URL
-3 con respecto a la semana pasada
8
Hashes
+2 con respecto a la semana pasada
15
IP
Sin variación con respecto a la semana pasada
104
Vulnerabilidades
+98 con respecto a la semana pasada
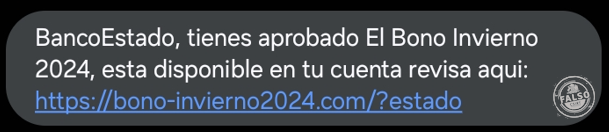
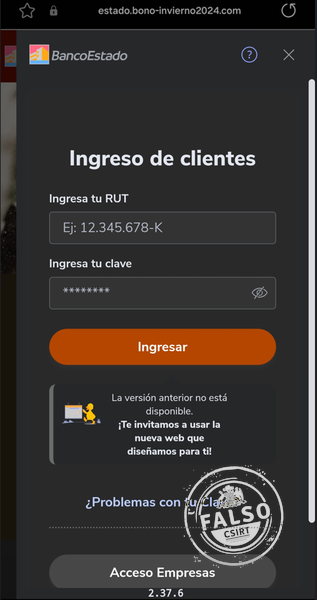
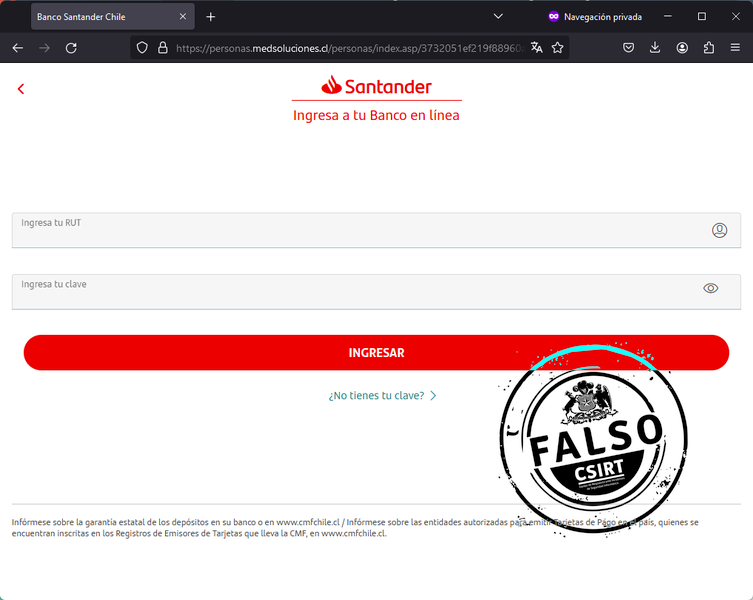
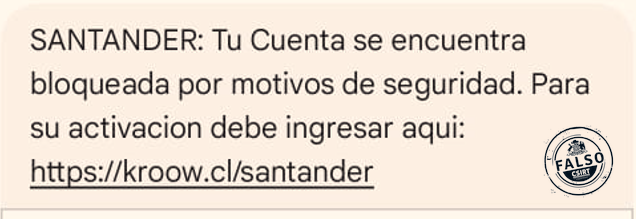
Phishing
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 104. 21. 14. 22 | IP sitio falso |
| URL | https: //bono-invierno2024. com/?estado | URL sitio falso |
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 194. 147. 71. 214 | IP sitio falso |
| URL | https: //kroow. cl/santander | URL redirección |
| URL | https: //personas. medsoluciones. cl/personas/index. asp/3732051ef219f88960a35bdbb856b49b | URL sitio falso |
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
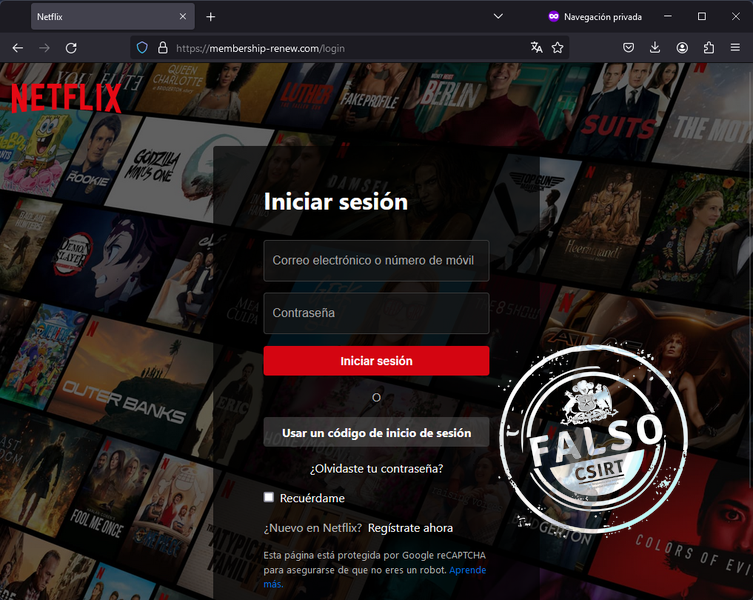
| IPv4 | 172. 67. 171. 150 | IP sitio falso |
| IPv4 | 54. 238. 185. 72 | IP SMTP |
| dev@kotsu. do | Correo de salida | |
| URL | https: //membership-app. com/log/ | URL redireccion |
| URL | https: //membership-renew. com/login | URL sitio falso |
| Asunto Email | Recordatorio: actualice su método de pago. | Asunto correo |
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
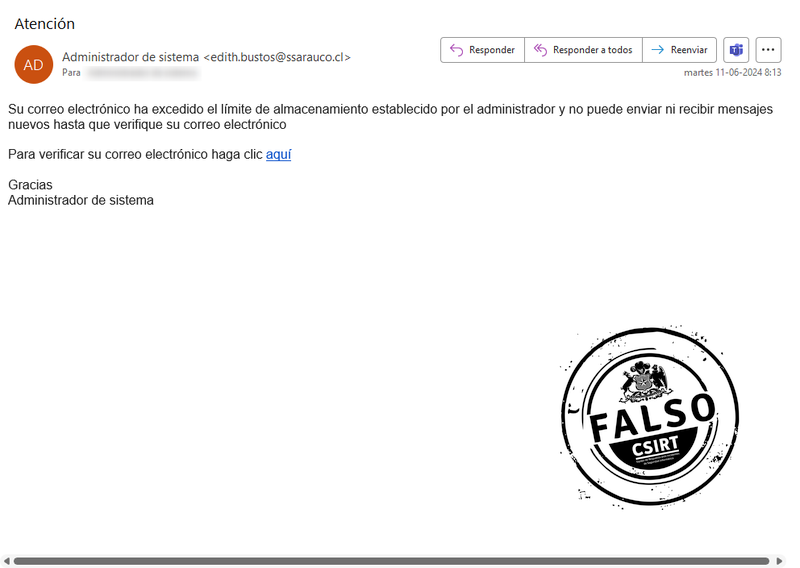
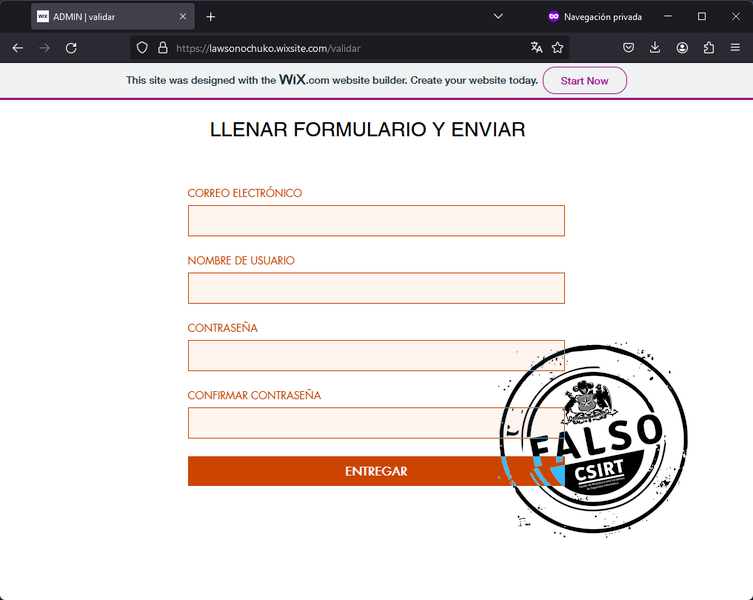
| IP:Puerto | 200. 6. 120. 54: 36844 | IP SMTP |
| IPv4 | 34. 117. 60. 144 | IP sitio falso |
| edith. bustos@ssarauco. cl | Correo de salida | |
| URL | https: //lawsonochuko. wixsite. com/validar | URL sitio falso |
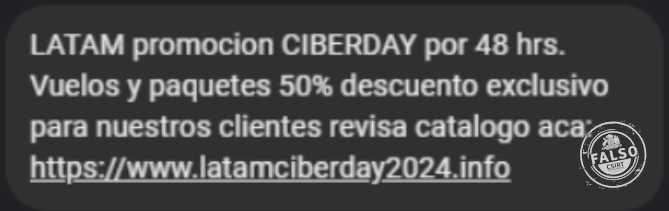
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
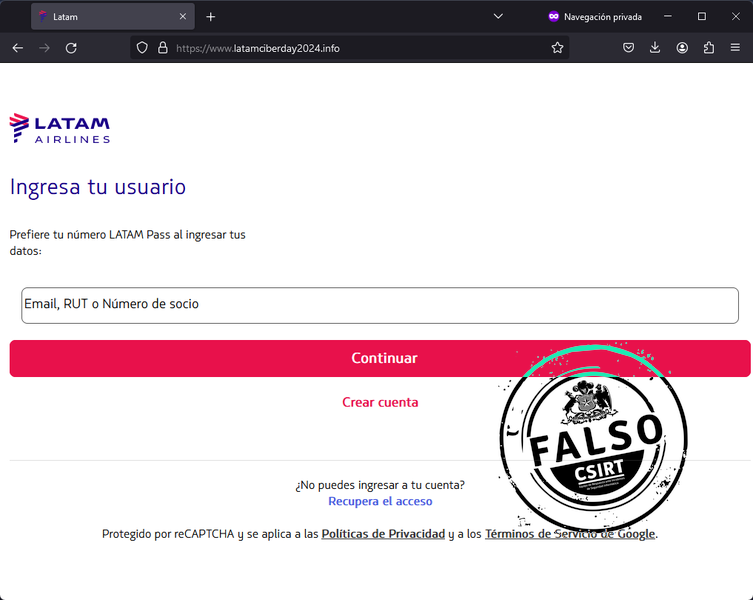
| IPv4 | 104. 21. 89. 65 | IP sitio falso |
| URL | https: //www. latamciberday2024. info/ | URL sitio falso |
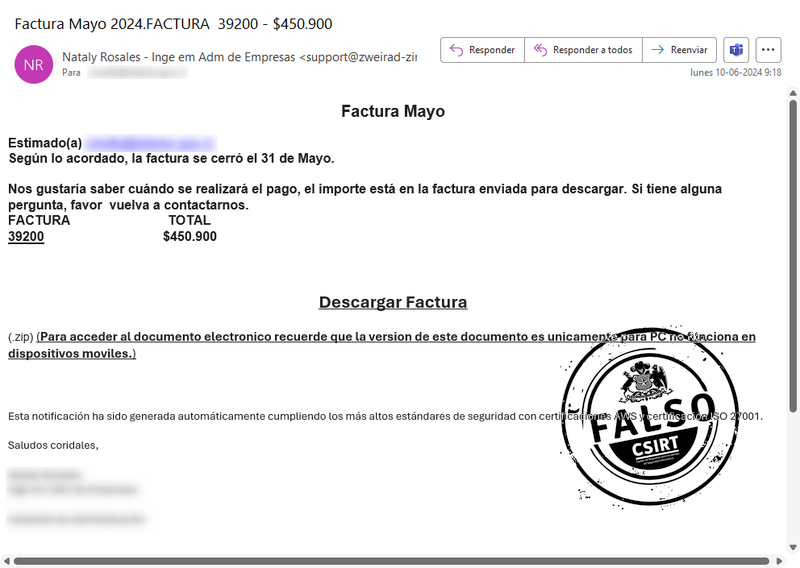
Suplantación con malware
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 103. 179. 191. 151 | IP SMTP |
| IPv4 | 116. 203. 200. 128 | IP SMTP |
| IPv4 | 138. 201. 59. 106 | IP SMTP |
| IPv4 | 149. 88. 90. 3 | IP SMTP |
| IPv4 | 162. 19. 171. 108 | IP SMTP |
| IPv4 | 195. 56. 241. 8 | IP SMTP |
| IPv4 | 34. 117. 186. 192 | Whois |
| SHA256 | 36a9e7f1c95b82ffb99743e0c5c4ce95d83c9a430aac59f84ef3cbfab6145068 | b.txt |
| IPv4 | 38. 54. 108. 15 | IP SMTP |
| SHA256 | 48c4eb69604e1551bab0fcad10c4a7056b2cf6342f6a244527967ea431490893 | 5df9b0.rbs |
| IPv4 | 50. 116. 35. 185 | Comando y control |
| SHA256 | 53a61793cb027c051a7acc8e2f53adaa717fb273dd461f7a4f8094971faadf20 | json[1].json |
| SHA256 | 5d2bcd4a1d967d54b3d1b304d16e7c74204ca383a63eedfed20da24b18aec17f | facturafechadamayo.msi |
| SHA256 | 7e3f309fc3a238119ee9e5f7b7a149a2125cbf327b60deef9c5cc82f7547191a | facturafechadamayo.zip |
| SHA256 | 7e643c188a1ee3b0251b7dfcab000b7c48fd840eff35189e8a45901852e3910a | ssleay32.dll |
| SHA256 | cc684e8981b8b0089b157abbabacfe4c6fadef15624ef53ebb7108b76b524d86 | 5df9af.rbs |
| SHA256 | e28e34fbdaff077669586dcdb4e10f0ba2ca6c9973ed4d372a5c3ec3b8ad20e7 | libeay32.dll |
| Asunto Email | Factura Mayo 2024. FACTURA 39200 - $450. 900 | Asunto correo |
| support@anteni. info | Correo de salida | |
| support@ciottociotto. it | Correo de salida | |
| support@dailyxetai. vn | Correo de salida | |
| support@dybi. hu | Correo de salida | |
| support@xiaoguoeducation. com | Correo de salida | |
| support@zweirad-zimmermann. com | Correo de salida |
Vulnerabilidades

Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-30070 | 7.5 | |
| CVE-2024-30069 | 4.7 | |
| CVE-2024-30068 | 8.8 | |
| CVE-2024-37325 | 8.1 | |
| CVE-2024-35265 | 7.0 | |
| CVE-2024-35263 | 5.7 | |
| CVE-2024-35255 | 5.5 | |
| CVE-2024-35254 | 7.1 | |
| CVE-2024-35253 | 4.4 | |
| CVE-2024-35252 | 7.5 | |
| CVE-2024-35250 | 7.8 | |
| CVE-2024-35249 | 8.8 | |
| CVE-2024-35248 | 7.3 | |
| CVE-2024-30104 | 7.8 | |
| CVE-2024-30103 | 8.8 | |
| CVE-2024-30102 | 7.3 | |
| CVE-2024-30101 | 7.5 | |
| CVE-2024-30100 | 7.8 | |
| CVE-2024-30099 | 7.0 | |
| CVE-2024-30097 | 8.8 | |
| CVE-2024-30094 | 7.8 | |
| CVE-2024-30093 | 7.3 | |
| CVE-2024-30091 | 7.8 | |
| CVE-2024-30090 | 7.0 | |
| CVE-2024-30089 | 7.8 | |
| CVE-2024-30088 | 7.0 | |
| CVE-2024-30096 | 5.5 | |
| CVE-2024-30095 | 7.8 | |
| CVE-2024-30087 | 7.8 | |
| CVE-2024-30086 | 7.8 | |
| CVE-2024-30085 | 7.8 | |
| CVE-2024-30084 | 7.0 | |
| CVE-2024-30083 | 7.5 | |
| CVE-2024-30082 | 7.8 | |
| CVE-2024-30080 | 9.8 | |
| CVE-2024-30078 | 8.8 | |
| CVE-2024-30077 | 8.0 | |
| CVE-2024-30076 | 6.8 | |
| CVE-2024-30075 | 8.0 | |
| CVE-2024-30067 | 5.5 | |
| CVE-2024-30066 | 5.5 | |
| CVE-2024-30065 | 5.5 | |
| CVE-2024-30074 | 8.0 | |
| CVE-2024-30072 | 7.8 | |
| CVE-2024-30064 | 8.8 | |
| CVE-2024-30063 | 6.7 | |
| CVE-2024-30062 | 7.8 | |
| CVE-2024-30052 | 4.7 | |
| CVE-2024-29187 | 7.3 | |
| CVE-2024-29060 | 6.7 | |
| CVE-2023-50868 | 7.5 |

Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-23110 | 7.8 | 0.04% |
| CVE-2024-26010 | 7.5 | 0.04% |
| CVE-2023-46720 | 6.7 | 0.04% |
| CVE-2024-3661 | 8.8 | 0.05% |
| CVE-2024-23111 | 6.2 | 0.04% |

Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-28996 | 7.5 | 0.09% |
| CVE-2024-28999 | 6.4 | 0.09% |
| CVE-2024-29004 | 7.1 | 0.05% |
| CVE-2021-4321 | 5.4 | |
| CVE-2023-0215 | 7.5 | |
| CVE-2022-0778 | 7.5 | |
| CVE-2021-23840 | 7.5 | |
| CVE-2023-0286 | 7.4 | |
| CVE-2021-3712 | 7.4 | |
| CVE-2018-0732 | 7.5 | |
| CVE-2020-1971 | 5.9 | |
| CVE-2019-1559 | 5.9 | |
| CVE-2018-0737 | 5.9 | |
| CVE-2017-3736 | 6.5 |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-5830 | 0.04% | |
| CVE-2024-5831 | 0.04% | |
| CVE-2024-5832 | 0.04% | |
| CVE-2024-5833 | 0.04% | |
| CVE-2024-5834 | 0.04% | |
| CVE-2024-5835 | 0.04% | |
| CVE-2024-5836 | 0.04% | |
| CVE-2024-5837 | 0.04% | |
| CVE-2024-5838 | 0.04% | |
| CVE-2024-5839 | 0.04% | |
| CVE-2024-5840 | 0.04% | |
| CVE-2024-5841 | 0.04% | |
| CVE-2024-5842 | 0.04% | |
| CVE-2024-5843 | 0.04% | |
| CVE-2024-5844 | 0.04% | |
| CVE-2024-5845 | 0.04% | |
| CVE-2024-5846 | 0.04% | |
| CVE-2024-5847 | 0.04% |

Noticias

Ciberconsejos
Muro de la Fama
Puedes encontrar el muro de la fama en este enlace.