Boletín Semanal
06 de abril de 2024 a 12 de abril de 2024
7
URL
-6 con respecto a la semana pasada
10
Hashes
-2 con respecto a la semana pasada
15
IP
+7 con respecto a la semana pasada
198
Vulnerabilidades
+186 con respecto a la semana pasada
Phishing
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 135. 125. 205. 93 | IP SMTP |
| IPv4 | 162. 19. 152. 203 | IP SMTP |
| IPv4 | 162. 19. 152. 84 | IP SMTP |
| IPv4 | 162. 19. 153. 42 | IP SMTP |
| IPv4 | 162. 19. 248. 48 | IP SMTP |
| IPv4 | 162. 19. 249. 45 | IP SMTP |
| IPv4 | 51. 195. 44. 121 | IP SMTP |
| IPv4 | 51. 195. 44. 175 | IP SMTP |
| IPv4 | 51. 195. 44. 183 | IP SMTP |
| IPv4 | 51. 195. 46. 3 | IP SMTP |
| IPv4 | 51. 195. 47. 138 | IP SMTP |
| IPv4 | 51. 195. 47. 194 | IP SMTP |
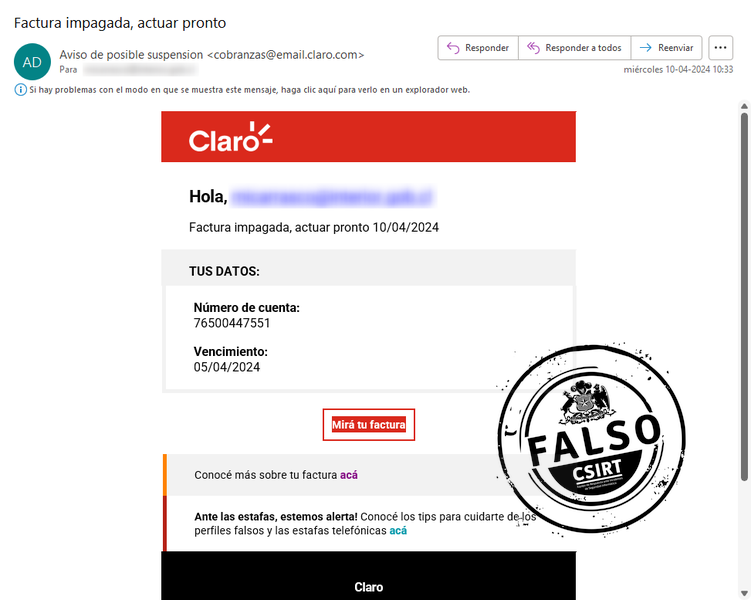
| Asunto Email | Factura impagada, actuar pronto | Asunto correo |
| URL | https: //cluprfacturagitalcionroma. norwayeast. cloudapp. azure. com/?facdigital-web/ConsultaClaro. aspx?nroFactura=9203-22988292&tokenValue=3233d6e527ebc123acf78373d3f0edb4135e3992 | Descarga de fichero |
| root@vps-019b8e8d. vps. ovh. net | Correo de salida | |
| root@vps-0bc5893f. vps. ovh. net | Correo de salida | |
| root@vps-11ee3f03. vps. ovh. net | Correo de salida | |
| root@vps-1b6060a8. vps. ovh. net | Correo de salida | |
| root@vps-21f3152c. vps. ovh. net | Correo de salida | |
| root@vps-2511e4bb. vps. ovh. net | Correo de salida | |
| root@vps-332abfad. vps. ovh. net | Correo de salida | |
| root@vps-35c7e3aa. vps. ovh. net | Correo de salida | |
| root@vps-3836ec22. vps. ovh. net | Correo de salida | |
| root@vps-38e7723d. vps. ovh. net | Correo de salida | |
| root@vps-4b975d3b. vps. ovh. net | Correo de salida | |
| root@vps-54ad4c72. vps. ovh. net | Correo de salida | |
| root@vps-5f4a1113. vps. ovh. net | Correo de salida | |
| root@vps-6d3bd7f0. vps. ovh. net | Correo de salida | |
| root@vps-7bb6712b. vps. ovh. net | Correo de salida | |
| root@vps-a27cf2b6. vps. ovh. net | Correo de salida | |
| root@vps-d3b19bbf. vps. ovh. net | Correo de salida | |
| root@vps-de3cb674. vps. ovh. net | Correo de salida | |
| root@vps-ed069c76. vps. ovh. net | Correo de salida | |
| root@vps-fd35fa7c. vps. ovh. net | Correo de salida |
Suplantación con malware
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
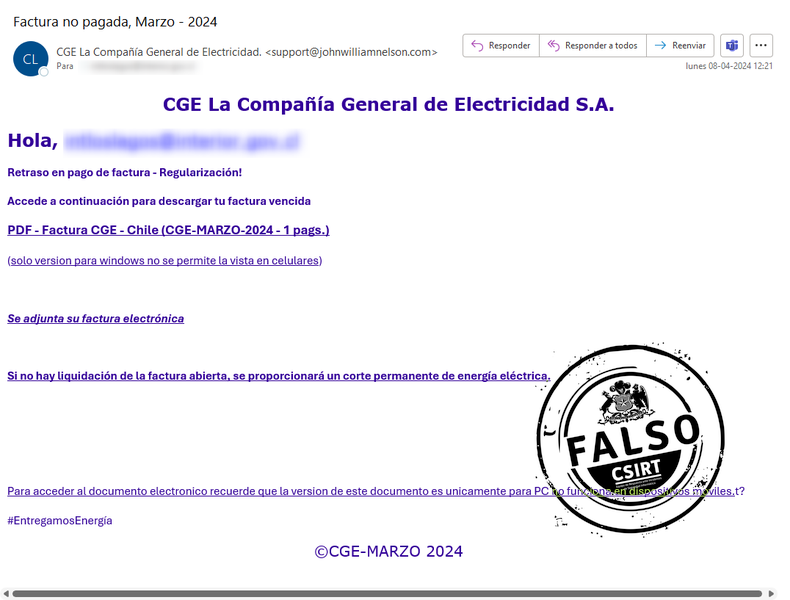
| SHA256 | 19ef6dcc8257fc55032aa97eb5613a8dc35cfd41bf4804d239ee349d03b7129c | factnuevamarzocgeboletaeletricidad.zip |
| IPv4 | 209. 59. 174. 255 | IP SMTP |
| IP:Puerto | 23. 239. 3. 218: 9091 | Comando y control |
| IPv4 | 34. 117. 186. 192 | Whois |
| SHA256 | 5cc97524d9ab2d29019d545b06f8ef8fcf5b9fb8ee257d7352a619f8950f5449 | factnuevamarzocgeboletaeletricidad.msi |
| SHA256 | 7e643c188a1ee3b0251b7dfcab000b7c48fd840eff35189e8a45901852e3910a | ssleay32.dll |
| SHA256 | e28e34fbdaff077669586dcdb4e10f0ba2ca6c9973ed4d372a5c3ec3b8ad20e7 | libeay32.dll |
| Dominio | https: //anchoriaatrade. com/nuevafactura/cgeletricidadboletamarzo/?hash={Email} | Redirección |
| URL | https: //digitalmukesh. info/fileman/factnuevamarzocgeboletaeletricidad. zip?282629426 | Descarga del fichero |
| support@augustineformayor. ca | Correo de salida | |
| support@banglachotigolpo. top | Correo de salida | |
| support@ikaglm. com | Correo de salida | |
| support@johnwilliamnelson. com | Correo de salida | |
| support@lot. ziy. cc | Correo de salida | |
| support@uncutmaza. club | Correo de salida | |
| support@uww-reg. ru | Correo de salida | |
| MITRE ATT&CK | T1012 | Consulta del Registro |
| MITRE ATT&CK | T1082 | Información del Sistema |
| MITRE ATT&CK | T1566. 002 | Acceso Inicial Mediante Phishing |
| MITRE ATT&CK | T1571 | Puerto no estándar |
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IP:Puerto | 185. 14. 202. 230: 587 | Comando y control |
| IPv4 | 31. 214. 169. 34 | IP SMTP |
| SHA256 | 34f838011c9242be21fc440f803dbc271a19e7cbf35dd585b68566df577e0cea | cotizacion_326092.exe |
| SHA256 | cbceb77aadc2e48791ffca911e04cb4fafad3d29545535b11c08d26e4dda971d | cotizacion_326092.r00 |
| Asunto Email | info@tadbirenergy. com | Correo de salida |
| Dominio | mail. olne. gr | Dominio |
| MITRE ATT&CK | T1005 | Datos del sistema local |
| MITRE ATT&CK | T1012 | Petición de los registros |
| MITRE ATT&CK | T1082 | Descubrimiento de la información del sistema |
| MITRE ATT&CK | T1497 | Evasión de la virtualización |
| MITRE ATT&CK | T1552. 001 | Credenciales en archivos |
| MITRE ATT&CK | T1552. 002 | Credenciales en el registro |
| MITRE ATT&CK | T1566. 002 | Mediante Phishing |
| MITRE ATT&CK | T1571 | Puerto no estándar |
| MITRE ATT&CK | T1574. 002 | Carga lateral de DLL |
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
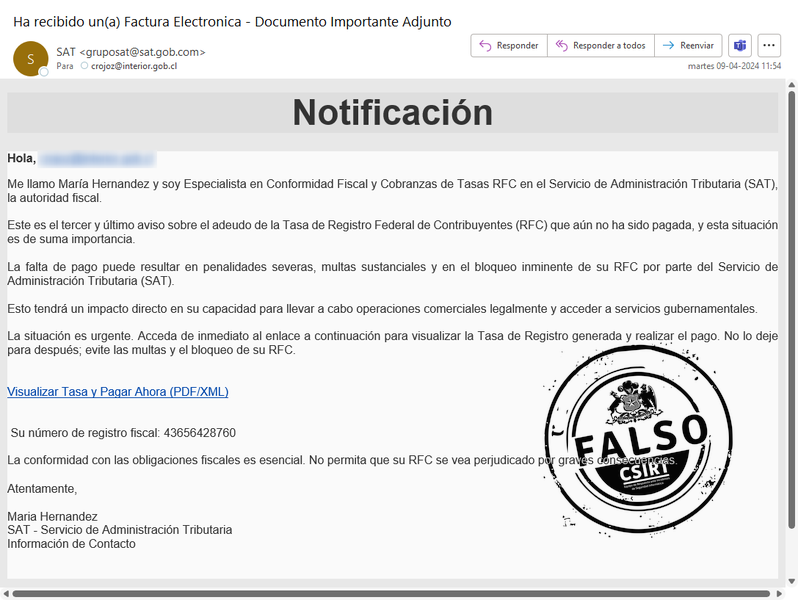
| IP:Puerto | 15. 228. 166. 44: 4917 | Comando y control |
| IP:Puerto | 15. 228. 166. 44: 50673/ModemSnaptfbAAppCrafters. xml | Payload |
| SHA256 | 1ec5aec6e629d8a9c3bf75e3c425bef10c25e1557283029745c434c7c9ee6389 | 6284DedallesDDUK7071FC-5355QDEH Emisor6051 Ref-ZILJ2286.exe |
| SHA256 | 67059e589ebd10e14640ccbe0c166a72eaef131697fe9ac63237609a23048b67 | AudioXpertXgrvModemMagic.exe |
| SHA256 | eeb1f2843f4e17352a324385145e58dfa6c843b74e5384fff643bc48be50faa2 | 7057CFDI_SAT6697NQCF.zip |
| SHA256 | f2d850025dd7b65c44d979ec74a3f5a77e1c15b4070812be5656887cee95dc59 | _________________________________________________510444299203.xml |
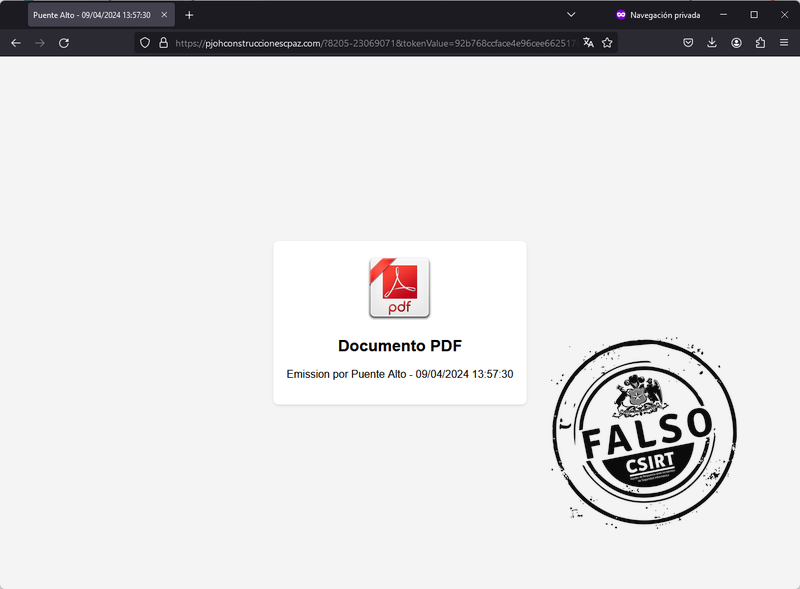
| URL | https: //pjohconstruccionescpaz. com/?8205-23069071&tokenValue=92b768ccface4e96cee662517800b208f88ff796 | Descarga del Fichero |
| URL | https: //uc33c855fe0b796d9b057399e710. dl. dropboxusercontent. com/cd/0/get/CQtKInASZ8XRqaQlWUmjguBq_hp2vsVA8zimuD-tsYXTGb_xMLo5W9Log6cozAZBz0uCZ0w_syv518kOKOXh-GIkY7BlMxdfgm4rWRRfDmhENWG1rECDYkRt8LpDvwQGIrH6XgXEyVzzyTGsLx-3FucR/file?dl=1# | Comprobación de la descarga |
| URL | https: //www. dropbox. com/scl/fi/dzsshpkfmu4ekkpo6t081/5839CFDI_SAT2511SORR. zip?rlkey=uurswnjggmrnsrwcb8o3e777n&dl=1 | Contenedor del malware |
| MITRE ATT&CK | T1012 | Consulta del Registro |
| MITRE ATT&CK | T1016 | Detección de la configuración de red del sistema |
| MITRE ATT&CK | T1059. 001 | PowerShell |
| MITRE ATT&CK | T1082 | Descubrimiento de información del sistema |
| MITRE ATT&CK | T1204. 002 | Archivo malicioso |
| MITRE ATT&CK | T1518 | Descubrimiento de programas |
| MITRE ATT&CK | T1552. 001 | Credenciales en archivos |
| MITRE ATT&CK | T1566. 002 | Mediante Phishing |
| MITRE ATT&CK | T1571 | Puerto no estándar |
Vulnerabilidades
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-21894 | 8.2 | |
| CVE-2024-22052 | 7.5 | |
| CVE-2024-22053 | 8.2 | |
| CVE-2024-22023 | 5.3 |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-20665 | 6.1 / 5.3 | |
| CVE-2024-20669 | 6.7 / 5.8 | |
| CVE-2024-20670 | 8.1 / 7.1 | |
| CVE-2024-20678 | 8.8 / 7.7 | |
| CVE-2024-20685 | 5.9 / 5.2 | |
| CVE-2024-20688 | 7.1 / 6.2 | |
| CVE-2024-20689 | 7.1 / 6.2 | |
| CVE-2024-20693 | 7.8 / 6.8 | |
| CVE-2024-21322 | 7.2 / 6.3 | |
| CVE-2024-21323 | 8.8 / 7.7 | |
| CVE-2024-21324 | 7.2 / 6.3 | |
| CVE-2024-21409 | 7.3 / 6.4 | |
| CVE-2024-21424 | 6.5 / 5.7 | |
| CVE-2024-21447 | 7.8 / 6.8 | |
| CVE-2024-2201 | 4.7 / 4.1 | |
| CVE-2024-23593 | 7.8 / 6.8 | |
| CVE-2024-23594 | 6.4 / 5.6 | |
| CVE-2024-26158 | 7.8 / 6.8 | |
| CVE-2024-26168 | 6.8 / 5.9 | |
| CVE-2024-26171 | 6.7 / 5.8 | |
| CVE-2024-26172 | 5.5 / 4.8 | |
| CVE-2024-26175 | 7.8 / 6.8 | |
| CVE-2024-26179 | 8.8 / 7.7 | |
| CVE-2024-26180 | 8.0 / 7.0 | |
| CVE-2024-26183 | 6.5 / 5.7 | |
| CVE-2024-26189 | 8.0 / 7.0 | |
| CVE-2024-26193 | 6.4 / 5.9 | |
| CVE-2024-26194 | 7.4 / 6.4 | |
| CVE-2024-26195 | 7.2 / 6.3 | |
| CVE-2024-26200 | 8.8 / 7.7 | |
| CVE-2024-26202 | 7.2 / 6.3 | |
| CVE-2024-26205 | 8.8 / 7.7 | |
| CVE-2024-26207 | 5.5 / 4.8 | |
| CVE-2024-26208 | 7.2 / 6.3 | |
| CVE-2024-26209 | 5.5 / 4.8 | |
| CVE-2024-26210 | 8.8 / 7.7 | |
| CVE-2024-26211 | 7.8 / 6.8 | |
| CVE-2024-26212 | 7.5 / 6.5 | |
| CVE-2024-26213 | 7.0 / 6.1 | |
| CVE-2024-26214 | 8.8 / 7.7 | |
| CVE-2024-26215 | 7.5 / 7.2 | |
| CVE-2024-26216 | 7.3 / 6.4 | |
| CVE-2024-26217 | 5.5 / 4.8 | |
| CVE-2024-26218 | 7.8 / 6.8 | |
| CVE-2024-26219 | 7.5 / 6.5 | |
| CVE-2024-26220 | 5.0 / 4.4 | |
| CVE-2024-26221 | 7.2 / 6.3 | |
| CVE-2024-26222 | 7.2 / 6.3 | |
| CVE-2024-26223 | 7.2 / 6.3 | |
| CVE-2024-26224 | 7.2 / 6.3 | |
| CVE-2024-26226 | 6.5 / 5.7 | |
| CVE-2024-26227 | 7.2 / 6.3 | |
| CVE-2024-26228 | 7.8 / 6.8 | |
| CVE-2024-26229 | 7.8 / 6.8 | |
| CVE-2024-26230 | 7.8 / 6.8 | |
| CVE-2024-26231 | 7.2 / 6.3 | |
| CVE-2024-26232 | 7.3 / 6.4 | |
| CVE-2024-26233 | 7.2 / 6.3 | |
| CVE-2024-26234 | 6.7 / 5.8 | |
| CVE-2024-26235 | 7.8 / 6.8 | |
| CVE-2024-26236 | 7.0 / 6.1 | |
| CVE-2024-26237 | 7.8 / 6.8 | |
| CVE-2024-26239 | 7.8 / 6.8 | |
| CVE-2024-26240 | 8.0 / 7.0 | |
| CVE-2024-26241 | 7.8 / 6.8 | |
| CVE-2024-26242 | 7.0 / 6.1 | |
| CVE-2024-26243 | 7.0 / 6.1 | |
| CVE-2024-26244 | 8.8 / 7.7 | |
| CVE-2024-26245 | 7.8 / 6.8 | |
| CVE-2024-26248 | 7.5 / 6.5 | |
| CVE-2024-26250 | 6.7 / 5.8 | |
| CVE-2024-26251 | 6.8 / 6.5 | |
| CVE-2024-26252 | 6.8 / 5.9 | |
| CVE-2024-26253 | 6.8 / 5.9 | |
| CVE-2024-26254 | 7.5 / 6.5 | |
| CVE-2024-26255 | 5.5 / 4.8 | |
| CVE-2024-26256 | 7.8 / 6.8 | |
| CVE-2024-26257 | 7.8 / 7.5 | |
| CVE-2024-28896 | 7.5 / 6.5 | |
| CVE-2024-28897 | 6.8 / 5.9 | |
| CVE-2024-28898 | 6.3 / 5.5 | |
| CVE-2024-28900 | 5.5 / 4.8 | |
| CVE-2024-28901 | 5.5 / 4.8 | |
| CVE-2024-28902 | 5.5 / 4.8 | |
| CVE-2024-28903 | 6.7 / 5.8 | |
| CVE-2024-28904 | 7.8 / 6.8 | |
| CVE-2024-28905 | 7.8 / 6.8 | |
| CVE-2024-28906 | 8.8 / 7.7 | |
| CVE-2024-28907 | 7.8 / 6.8 | |
| CVE-2024-28908 | 8.8 / 7.7 | |
| CVE-2024-28909 | 8.8 / 7.7 | |
| CVE-2024-28910 | 8.8 / 7.7 | |
| CVE-2024-28911 | 8.8 / 7.7 | |
| CVE-2024-28912 | 8.8 / 7.7 | |
| CVE-2024-28913 | 8.8 / 7.7 | |
| CVE-2024-28914 | 8.8 / 7.7 | |
| CVE-2024-28915 | 8.8 / 7.7 | |
| CVE-2024-28917 | 6.2 / 5.4 | |
| CVE-2024-28919 | 6.7 / 5.8 | |
| CVE-2024-28920 | 7.8 / 6.8 | |
| CVE-2024-28921 | 6.7 / 5.8 | |
| CVE-2024-28922 | 4.1 / 3.6 | |
| CVE-2024-28923 | 6.4 / 5.6 | |
| CVE-2024-28924 | 6.7 / 5.8 | |
| CVE-2024-28925 | 8.0 / 7.0 | |
| CVE-2024-28926 | 8.8 / 7.7 | |
| CVE-2024-28927 | 8.8 / 7.7 | |
| CVE-2024-28929 | 8.8 / 7.7 | |
| CVE-2024-28930 | 8.8 / 7.7 | |
| CVE-2024-28931 | 8.8 / 7.7 | |
| CVE-2024-28932 | 8.8 / 7.7 | |
| CVE-2024-28933 | 8.8 / 7.7 | |
| CVE-2024-28934 | 8.8 / 7.7 | |
| CVE-2024-28935 | 8.8 / 7.7 | |
| CVE-2024-28936 | 8.8 / 7.7 | |
| CVE-2024-28937 | 8.8 / 7.7 | |
| CVE-2024-28938 | 8.8 / 7.7 | |
| CVE-2024-28939 | 8.8 / 7.7 | |
| CVE-2024-28940 | 8.8 / 7.7 | |
| CVE-2024-28941 | 8.8 / 7.7 | |
| CVE-2024-28942 | 8.8 / 7.7 | |
| CVE-2024-28943 | 8.8 / 7.7 | |
| CVE-2024-28944 | 8.8 / 7.7 | |
| CVE-2024-28945 | 8.8 / 7.7 | |
| CVE-2024-29043 | 8.8 / 7.7 | |
| CVE-2024-29044 | 8.8 / 7.7 | |
| CVE-2024-29045 | 7.5 / 6.5 | |
| CVE-2024-29046 | 8.8 / 7.7 | |
| CVE-2024-29047 | 8.8 / 7.7 | |
| CVE-2024-29048 | 8.8 / 7.7 | |
| CVE-2024-29050 | 8.4 / 7.3 | |
| CVE-2024-29052 | 7.8 / 6.8 | |
| CVE-2024-29053 | 8.8 / 7.7 | |
| CVE-2024-29054 | 7.2 / 6.3 | |
| CVE-2024-29055 | 7.2 / 6.3 | |
| CVE-2024-29056 | 4.3 / 3.8 | |
| CVE-2024-29061 | 7.8 / 6.8 | |
| CVE-2024-29062 | 7.1 / 6.2 | |
| CVE-2024-29063 | 7.3 / 6.6 | |
| CVE-2024-29064 | 6.2 / 5.4 | |
| CVE-2024-29066 | 7.2 / 6.3 | |
| CVE-2024-29982 | 8.8 / 7.7 | |
| CVE-2024-29983 | 8.8 / 7.7 | |
| CVE-2024-29984 | 8.8 / 7.7 | |
| CVE-2024-29985 | 8.8 / 7.7 | |
| CVE-2024-29988 | 8.8 / 8.2 | |
| CVE-2024-29989 | 8.4 / 7.3 | |
| CVE-2024-29990 | 9.0 / 8.1 | |
| CVE-2024-29992 | 5.5 / 5.3 | |
| CVE-2024-29993 | 8.8 / 7.7 |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2023-45590 | 9.4 | |
| CVE-2024-21756 | 8.6 | |
| CVE-2024-21755 | 8.6 | |
| CVE-2024-23671 | 7.9 | |
| CVE-2023-45588 | 7.8 | |
| CVE-2024-31492 | 7.8 | |
| CVE-2023-41677 | 7.5 | |
| CVE-2023-48784 | 6.1 | |
| CVE-2024-23662 | 5 |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-20758 | 9 | |
| CVE-2024-20759 | 8.1 | |
| CVE-2024-26046 | 5.4 | |
| CVE-2024-26047 | 5.4 | |
| CVE-2024-26079 | 5.4 | |
| CVE-2024-26084 | 5.4 | |
| CVE-2024-26087 | 5.4 | |
| CVE-2024-26097 | 5.4 | |
| CVE-2024-26098 | 5.4 | |
| CVE-2024-26122 | 5.4 | |
| CVE-2024-20778 | 5.4 | |
| CVE-2024-20779 | 5.4 | |
| CVE-2024-20780 | 5.4 | |
| CVE-2024-26076 | 5.3 | |
| CVE-2024-30271 | 7.8 | |
| CVE-2024-30272 | 7.8 | |
| CVE-2024-30273 | 7.8 | |
| CVE-2024-20798 | 5.5 | |
| CVE-2024-20771 | 5.5 | |
| CVE-2024-20737 | 5.5 | |
| CVE-2024-20770 | 5.5 | |
| CVE-2024-20766 | 5.5 | |
| CVE-2024-20772 | 7.8 |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-27899 | 8.8 | |
| CVE-2024-25646 | 7.7 | |
| CVE-2024-27901 | 7.2 | |
| CVE-2024-30218 | 6.5 | |
| CVE-2024-28167 | 6.5 | |
| CVE-2022-29613 | 6.5 | |
| CVE-2023-40306 | 6.1 | |
| CVE-2024-27898 | 5.3 | |
| CVE-2024-30214 | 4.8 | |
| CVE-2024-30215 | 4.8 | |
| CVE-2024-30216 | 4.3 | |
| CVE-2024-30217 | 4.3 |

Noticias

Ciberconsejos
Muro de la Fama
Puedes encontrar el muro de la fama en este enlace.