Boletín Semanal
20 de abril de 2024 a 26 de abril de 2024
13
URL
+1 con respecto a la semana pasada
3
Hashes
-1 con respecto a la semana pasada
15
IP
+2 con respecto a la semana pasada
61
Vulnerabilidades
-184 con respecto a la semana pasada
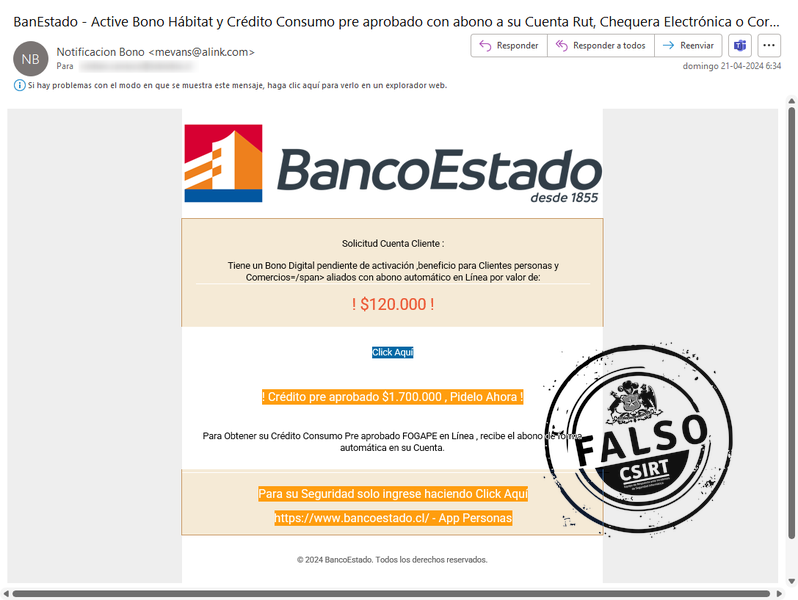
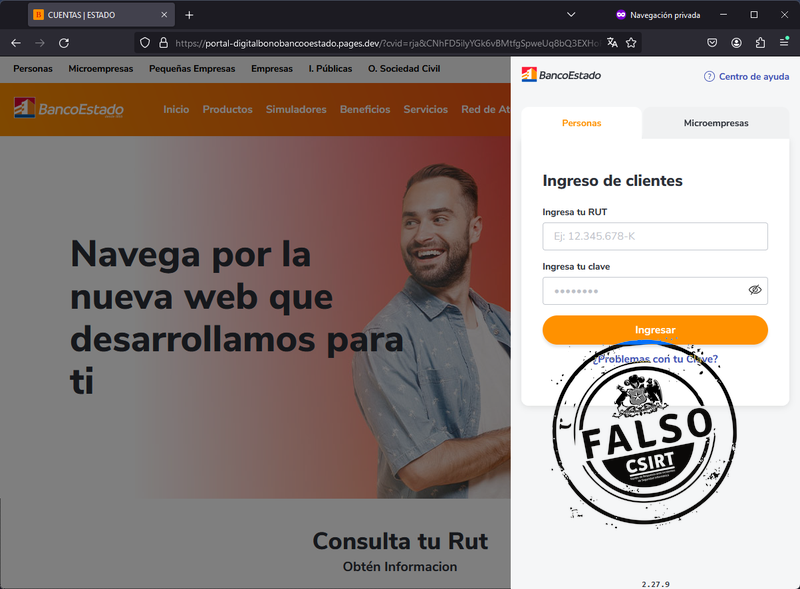
Phishing
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 122. 201. 66. 57 | IP sitio falso |
| IPv4 | 37. 60. 235. 206 | IP SMTP |
| apache@vmi1801713. contaboserver. net | Correo de salida | |
| URL | https: //fogape. larissakovalchuk. com/1713799490/imagenes/_personas/home/default. asp | URL sitio falso |
| URL | https: //temucoproduce. com/activacion/cuenta-nldo/ | URL redirección |
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 172. 66. 47. 116 | IP sitio falso |
| IP:Puerto | 208. 68. 187. 2: 46481 | IP SMTP |
| Asunto Email | BanEstado - Active Bono Hábitat y Crédito Consumo pre aprobado con abono a su Cuenta Rut, Chequera Electrónica o Corriente | Para ayuda Familiar en Banca en Linea | Asunto del correo electrónico |
| URL | http: //159. 65. 156. 91/dc8a63028568ce934158852be92c13c9/db44ec749ab06ea44c53S/5ead2be--f8a12a42bb492/?k=KERT | URL sitio redirección |
| URL | https: //bit. ly/4cBQnRD | URL sitio redirección |
| URL | https: //portal-digitalbonobancooestado. pages. dev/?cvid=rja&CNhFD5ilyYGk6vBMtfgSpweUq8bQ3EXHoPLIaJcAZzV1sxTWrO9740ujmdKRn2 | URL sitio falso |
| mevans@alink. com | Correo de salida |
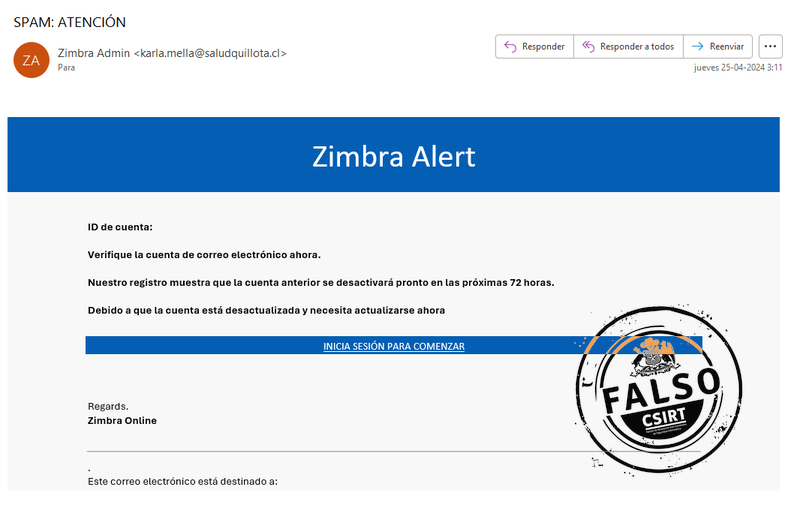
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 131. 108. 210. 21 | IP SMTP |
| IPv4 | 209. 94. 90. 1 | IP sitio falso |
| URL | https: //ipfs. io/ipfs/bafybeih4wwljr3lg6fxunpfgmjpqlwhihybtxvvbn5wesic6ii6wdjizfm/eso. com. mk. htm | URL sitio falso |
| karla. mella@saludquillota. cl | Correo de salida | |
| Asunto Email | SPAM: ATENCIÓN | Asunto correo electronico |
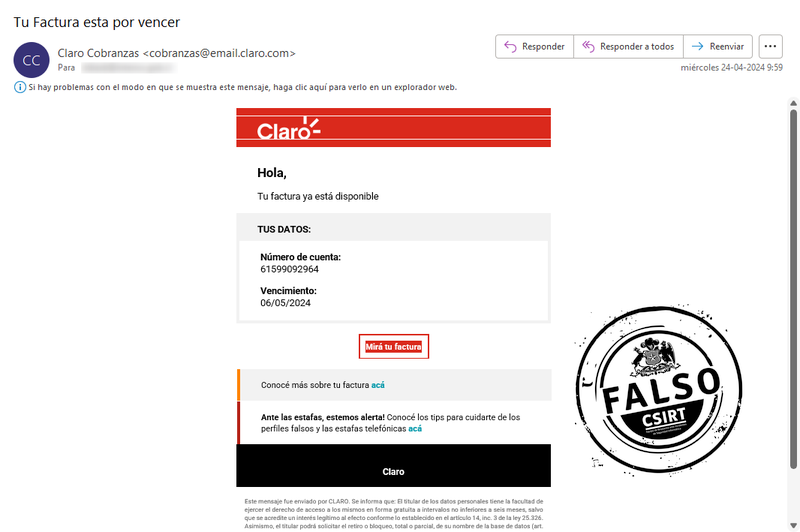
Suplantación con malware
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 198. 244. 232. 236 | IP SMTP |
| IPv4 | 198. 244. 232. 255 | IP SMTP |
| IPv4 | 208. 95. 112. 1 | Whois |
| SHA256 | 4c03891763e6c40c8610017c97a2611d8a4178803eee14b2fc7749819020168b | RVUF_ID_FAC#JELYOGQBCUHV.zip |
| IPv4 | 51. 38. 64. 91 | IP SMTP |
| IP:Puerto | 54. 207. 63. 172: 9416 | Comando y control |
| IPv4 | 54. 37. 17. 140 | IP SMTP |
| IPv4 | 54. 37. 18. 121 | IP SMTP |
| IPv4 | 54. 37. 18. 3 | IP SMTP |
| SHA256 | f05ca75ef01264185e8669b7818de091fc06d574deecc5af07f5645314e380cd | UHMH_Dedalles_KRXZ_Fact_IVBERTNZOKII.exe |
| SHA256 | f2d850025dd7b65c44d979ec74a3f5a77e1c15b4070812be5656887cee95dc59 | ______________________________________________________QNMTJGUKUOKGUOJM.xml |
| URL | http: //54. 207. 63. 172: 31430/NetBoostKJcXDataGuardTower. xml | URL descarga de segunda fase |
| URL | https: //ucfbff3aa5b84c6c8ca29720270a. dl. dropboxusercontent. com/cd/0/get/CRo8azg5EY5ZWLFPos3GEvc2avxhXU3J55g919ssLeRp6PXik1-vuuRsf-Z7Y6LUttdmlQbwls1zJAYMQYKWyEDQ6XL9RbjmS63kdiFC3QPpdibqjg1e2eM_Bx82awZckRRX7LaGENsy4YIQ_QfADfhR/file?dl=1# | URL comprobación de la descarga |
| URL | https: //unslfacturascperalt. norwayeast. cloudapp. azure. com/?facdigital-web/ConsultaClaro. aspx?nroFactura=9203-22988292&tokenValue=3233d6e527ebc123acf78373d3f0edb4135e3992 | URL de descarga |
| URL | https: //www. dropbox. com/scl/fi/vocsvd7jebye734rdpker/RVUF_ID_FAC-JELYOGQBCUHV. zip?rlkey=0tr8ghc8vtj0m2u3tlbdfabbn&st=llilydev&dl=1 | URL contenedora del archivo |
| root@vps-090492c0. vps. ovh. net | Correo de salida | |
| root@vps-19f22aa8. vps. ovh. net | Correo de salida | |
| root@vps-26816b6e. vps. ovh. net | Correo de salida | |
| root@vps-9732f21e. vps. ovh. net | Correo de salida | |
| root@vps-a2d5793a. vps. ovh. net | Correo de salida | |
| root@vps-ef63bc3d. vps. ovh. net | Correo de salida | |
| MITRE ATT&CK | T1012 | Consulta del Registro |
| MITRE ATT&CK | T1016 | Detección de la configuración de red del sistema |
| MITRE ATT&CK | T1082 | Descubrimiento de información del sistema |
| MITRE ATT&CK | T1204. 002 | Archivo malicioso |
| MITRE ATT&CK | T1518 | Descubrimiento de programas |
| MITRE ATT&CK | T1552. 001 | Credenciales en archivos |
| MITRE ATT&CK | T1566. 002 | Mediante phishing |
| MITRE ATT&CK | T1571 | Puerto no estandar |
Vulnerabilidades
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2021-21974 | 8.8 | 35,63% |
| CVE-2019-5544 | 9.8 | 3.27% |
| CVE-2020-3992 | 9.8 | 87,96% |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-20295 | 8.8 | 0,04% |
| CVE-2024-20356 | 8.7 | 0,04% |
| CVE-2024-20353 | 8.6 | 1,18% |
| CVE-2024-20359 | 6.0 | 1,18% |
| CVE-2024-20358 | 6.0 | 0,04% |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-22061 | 8.1 | |
| CVE-2024-23526 | 5.3 | |
| CVE-2024-23527 | 5.3 | |
| CVE-2024-23528 | 5.3 | |
| CVE-2024-23529 | 5.3 | |
| CVE-2024-23530 | 5.3 | |
| CVE-2024-23531 | 7.5 | |
| CVE-2024-23533 | 4.3 | |
| CVE-2024-23532 | 7.5 | |
| CVE-2024-23534 | 8.8 | |
| CVE-2024-23535 | 8.8 | |
| CVE-2024-24991 | 6.5 | |
| CVE-2024-24992 | 8.8 | |
| CVE-2024-24993 | 8.8 | |
| CVE-2024-24994 | 8.8 | |
| CVE-2024-24995 | 8.8 | |
| CVE-2024-24996 | 9.8 | |
| CVE-2024-24997 | 8.8 | |
| CVE-2024-24998 | 8.8 | |
| CVE-2024-24999 | 8.8 | |
| CVE-2024-25000 | 8.8 | |
| CVE-2024-27975 | 8.8 | |
| CVE-2024-27976 | 8.8 | |
| CVE-2024-27977 | 7.1 | |
| CVE-2024-27978 | 6.5 | |
| CVE-2024-27984 | 7.1 | |
| CVE-2024-29204 | 9.8 |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-3832 | 0.05% | |
| CVE-2024-3833 | 0.05% | |
| CVE-2024-3914 | 0.05% | |
| CVE-2024-3834 | 8.8 | 0.06% |
| CVE-2024-3837 | 8.8 | 0.06% |
| CVE-2024-3838 | 5.5 | 0.05% |
| CVE-2024-3839 | 6.5 | 0.05% |
| CVE-2024-3840 | 0.05% | |
| CVE-2024-3841 | 0.05% | |
| CVE-2024-3843 | 0.05% | |
| CVE-2024-3844 | 0.05% | |
| CVE-2024-3845 | 0.05% | |
| CVE-2024-3846 | 0.05% | |
| CVE-2024-3847 | 0.05% |
Vulnerabilidades
| ID | CVSS | EPSS |
|---|---|---|
| CVE-2024-3852 | 0.05% | |
| CVE-2024-3853 | 0.04% | |
| CVE-2024-3854 | 0.05% | |
| CVE-2024-3855 | 0.04% | |
| CVE-2024-3856 | 0.04% | |
| CVE-2024-3857 | 0.05% | |
| CVE-2024-3858 | 0.04% | |
| CVE-2024-3859 | 0.05% | |
| CVE-2024-3860 | 0.04% | |
| CVE-2024-3861 | 0.05% | |
| CVE-2024-3862 | 0.04% | |
| CVE-2024-3863 | 0.05% |
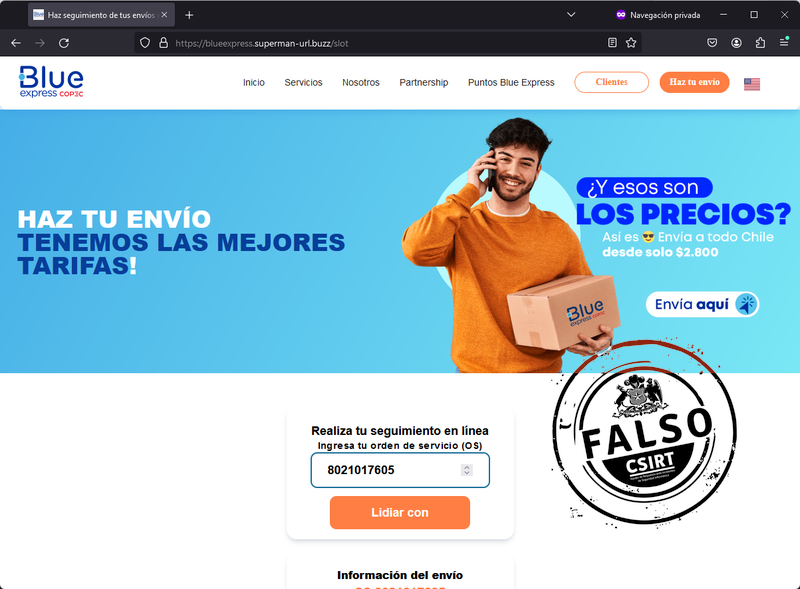
Falsificación
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 162. 62. 53. 33 | IP sitio falso |
| URL | https: //blueexpress. superman-url. buzz/slot | URL sitio falso |
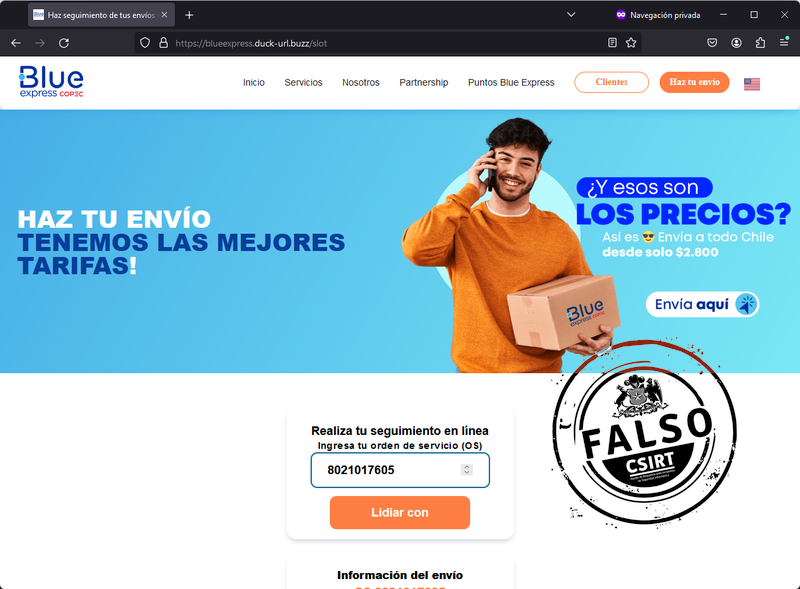
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 162. 62. 53. 33 | IP sitio falso |
| URL | https: //blueexpress. duck-url. buzz/slot | URL sitio falso |
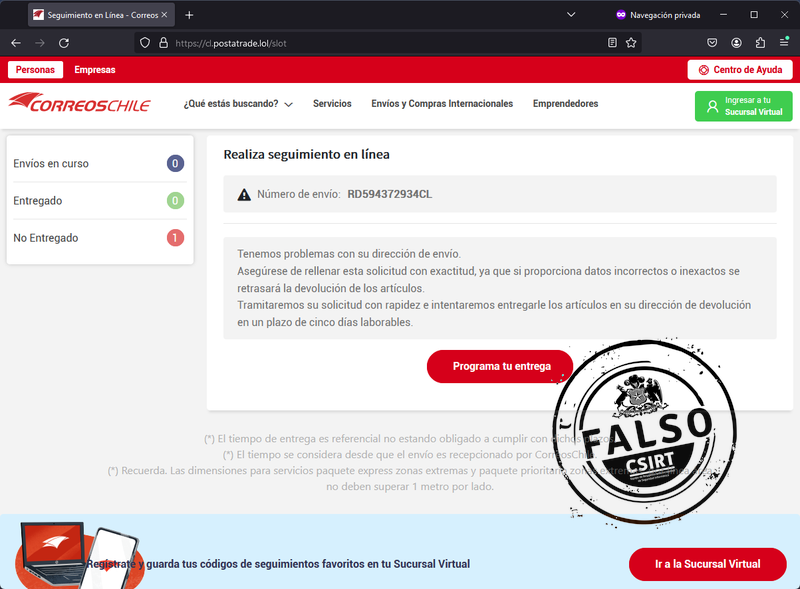
Indicadores de Compromiso
| Tipo | Valor | Comentario |
|---|---|---|
| IPv4 | 162. 62. 53. 33 | IP sitio falso |
| URL | https: //cl. postatrade. lol/slot | URL sitio falso |

Noticias

Ciberconsejos
No se publicaron consejos esta semana.
Muro de la Fama
Puedes encontrar el muro de la fama en este enlace.